Full Course on Ethical Hacking: Networking & Python Programming
This video is a full course on ethical hacking, covering topics such as networking, Python programming, and information gathering.
00:00:08 This course provides a 12-hour practical introduction to ethical hacking, covering topics such as note keeping, computer networking, Python, and the ethical hacker methodology. The instructor discusses the different types of assessments and the skills needed for a successful career in ethical hacking.
Ethical hacking is a booming industry with career opportunities for people from various backgrounds.
The video covers the topics and skills required to become a successful ethical hacker, including technical knowledge, note-keeping, and soft skills.
The importance of effective note-keeping and the use of tools like KeepNote and GreenShot for documenting findings and taking screenshots during assessments.
00:36:04 This video provides a comprehensive overview of IP addresses, subnetting, the OSI model, and common ports and protocols. The presenter explains the concepts in a clear and concise manner, making it easy to understand and follow along.
🔒 Having a strong networking foundation is essential for ethical hacking and penetration testing.
🌐 IP addresses are used to communicate over layer 3, and there are two main types: IPv4 and IPv6.
🔍 TCP and UDP are two protocols used in networking, with TCP being connection-oriented and UDP being connectionless.
🖥️ The OSI model provides a framework for understanding network communication and troubleshooting.
🔒 Subnetting is a method used to divide IP address ranges into smaller subnetworks.
01:11:18 This video provides an introduction to subnetting, explaining the concept of subnets and how to calculate subnet masks and host ranges. It also discusses the use of virtual machines for creating lab environments and demonstrates the installation of Kali Linux on a virtual machine.
Subnets are represented by ones and zeros, with the ones determining the value of the subnet mask.
The subnet mask is important for determining various factors in a network.
Different subnet masks allow for different numbers of hosts in a network.
01:46:21 This video provides a full course on ethical hacking using Kali Linux. It covers topics such as setting up virtual machines, navigating the file system, changing file permissions, adding users, and network commands.
🔑 The video covers the setup and configuration of Kali Linux and its virtual machine.
🚀 The video explains how to navigate the file system and change file permissions in Linux.
👥 The video demonstrates how to add users and manage their permissions in Linux.
🌐 The video introduces network commands for viewing and managing network interfaces in Linux.
02:24:28 This video is a tutorial on ethical hacking, focusing on networking commands such as ping, arp, netstat, and route. It also covers the use of tools like ifconfig, ip, and gedit for creating and editing files.
The video is about ethical hacking and covers various networking commands, such as ifconfig, iwconfig, ping, arp, netstat, and route.
It explains how to view, create, and edit files using commands like echo, cat, touch, nano, and gedit.
The video also introduces scripting with bash and demonstrates how to write a ping sweep script to ping multiple IP addresses within a subnet.
03:00:27 Learn about variables and methods in Python, including how to define variables, use string methods, perform math operations, and convert data types.
📝 Ethical hacking is a subject being discussed in the video.
🎥 The video teaches how to create a script to automate IP scanning and device discovery.
📚 The video also covers the basics of Python programming, including strings, math operations, variables, and methods.
03:36:36 Title: Ethical Hacking in 12 Hours - Full Course - Learn to Hack!. Transcript: Summary: The video explains how to use variables, functions, and conditional statements in Python programming. It covers topics such as adding and printing variables, defining functions, using boolean expressions, and implementing conditional statements for decision-making. The examples provided include calculating age, buying drinks based on age and money, and creating a list of favorite movies. The video serves as a beginner's guide to Python programming.
🎥 Lists are data structures that allow for grouping of elements.
🔢 Lists use numerical indexing, starting from 0, to access elements within the list.
📝 Lists can be sliced or accessed using a range of indices.
04:15:25 Title: Ethical Hacking in 12 Hours - Full Course - Learn to Hack!. Summary: This video provides an overview of various concepts in Python, including lists, tuples, loops, importing modules, advanced strings, and dictionaries.
📝 Dictionaries consist of key-value pairs
📄 Keys in dictionaries are unique and used to access values
➕ New key-value pairs can be added using the format 'dictionary[key] = value'
🔄 Values in dictionaries can be updated using the format 'dictionary[key] = new_value'
🔍 Values in dictionaries can be accessed using the 'get' method
04:54:12 Learn about the different stages of ethical hacking and how to gather information passively. Focus on physical and social reconnaissance, web and host assessments, and data breaches.
📚 Summary of the video's transcription:
🔑 Passive Reconnaissance: Gathering information on the physical and social aspects of a target, such as location, employees, and job information.
🖥️ Web and Host Assessment: Validating targets, finding subdomains, and fingerprinting web servers and open ports.
🔐 Data Breaches: Utilizing breached credentials and leaked data to gain access to networks and systems.
05:33:47 Learn about ethical hacking and how to gather information through tools like Hunter.io and D-Hash. See examples of breached credentials and how they can be utilized in an investigation.
🔍 The video is about ethical hacking and focuses on information gathering.
💻 Bug crowd is introduced as a platform for bug bounties, and tesla.com is mentioned as a target.
📧 Several tools and techniques for discovering email addresses and verifying them are shown.
06:06:03 A tutorial video on ethical hacking, focusing on data collection and analysis. The instructor demonstrates tools like Sublister, WhatWeb, and Burp Suite to gather information on subdomains, technologies, and web traffic.
🔍 The video is about ethical hacking and the process of gathering information for a penetration test.
🌐 The speaker discusses different techniques for searching and gathering data, such as searching for passwords and usernames and using tools like Sublister and Burp Suite.
💡 The video emphasizes the importance of subdomain hunting, gathering information about the technologies used on websites, and utilizing tools like Wappalyzer and WhatWeb.
06:39:02 Summary: This video is a full course on ethical hacking that covers topics such as using Google for research, scanning and enumeration, and stealth scanning with Nmap. It emphasizes the importance of information gathering and the use of tools like Nmap and netdiscover. Alternative Title: Full Course on Ethical Hacking: Using Google, Nmap, and Netdiscover
🔑 The video is about ethical hacking and focuses on using tools like Burp Suite and Google to gather information for penetration testing.
🌐 The importance and effectiveness of using Google for research and finding solutions to problems in the field of IT is highlighted.
🔍 The video also explains various techniques for using Google search operators to narrow down search results and find specific information, such as subdomains and file types.
07:14:20 Title: Ethical Hacking in 12 Hours - Full Course - Learn to Hack!. Summary: The video covers enumeration and scanning techniques for ethical hacking, focusing on web and SMB ports. It emphasizes the importance of information disclosure and version enumeration.
The video discusses the process of enumerating open ports and exploiting vulnerabilities on a target machine.
The speaker focuses on web servers running Apache and explores potential vulnerabilities related to outdated versions of Apache and SSL.
The video also covers SMB file shares and the importance of enumerating SMB versions and potential exploits.
07:53:42 Title: Ethical Hacking in 12 Hours - Full Course - Learn to Hack!. Summary: This video provides an overview of ethical hacking, including scanning for vulnerabilities in network protocols. It demonstrates using tools like Nmap and Nessus to identify potential security weaknesses.
The video is about using Nessus, a vulnerability scanner, to perform network scans and identify vulnerabilities.
The video shows how to install and configure Nessus and demonstrates how to create and launch network scans.
Different types of scans, such as basic network scans and advanced scans, are explained, along with their respective settings and options.
08:33:11 The video is a tutorial on ethical hacking and focuses on using the Nessus vulnerability scanner for scanning web applications and exploiting vulnerabilities. It also covers the concepts of reverse shell, bind shell, and stage versus non-stage payloads.
The video is about ethical hacking and the process of scanning for vulnerabilities and exploiting them.
The video demonstrates the use of tools like Nessus and Metasploit for scanning and exploitation.
The importance of post-exploitation techniques and enumerating the target system is highlighted.
09:13:08 The video provides a practical demonstration of ethical hacking techniques, including brute force attacks and credential stuffing. It also discusses the importance of privilege escalation and demonstrates how to import and attack a Windows machine.
🔒 Penetration testing involves being as loud as possible to test security measures.
🔑 Brute force attacks can be used to crack passwords and gain unauthorized access.
🔐 Credential stuffing is the injection of breach account credentials to take over accounts.
09:47:08 Summary: The video demonstrates how to enumerate and exploit vulnerabilities in a Windows 7 machine using SMB and the EternalBlue exploit. The process involves scanning, using Metasploit and manual methods to gain access to the machine.
🔑 The video discusses the process of ethical hacking, focusing on the enumeration of SMB (Server Message Block) vulnerabilities and the exploitation of the EternalBlue exploit.
💻 The presenter demonstrates the use of tools like Metasploit and a manual method to identify and exploit vulnerabilities in a target machine running Windows 7.
🔒 The video emphasizes the importance of obtaining permission before conducting a penetration test and highlights the potential risks of running exploits without proper caution in critical environments.
10:19:36 Learn ethical hacking through a 12-hour full course. Discover techniques like directory busting and privilege escalation to gain unauthorized access.
🔒 Ethical hacking involves testing and securing computer systems and networks.
⌨️ The video discusses various tools and techniques used in ethical hacking, such as hashcat, directory busting, and privilege escalation.
🔐 The importance of securing websites and avoiding vulnerabilities is highlighted through demonstrations of exploiting a file upload feature and finding a mysql password.
10:53:01 Learn the process of ethical hacking, including port scanning, web page enumeration, local file inclusion, and privilege escalation in a Linux machine. Use Burp Suite to brute force the login credentials of a Jenkins application.
📺 By analyzing different ports, the ethical hacker discovers a bolt installation error and a PHP info page, indicating a Linux machine.
📲 The hacker mounts a network file share and finds a password-protected file, but is unable to crack it.
🤔 Using a local file inclusion vulnerability in Jenkins, the hacker attempts to gain access, but is unsuccessful in finding valid credentials.
💥 The hacker uses Burp Suite to perform a brute force attack on the Jenkins login page, trying multiple usernames and passwords.
11:29:37 Ethical Hacking in 12 Hours - Full Course - Learn to Hack! A video tutorial on ethical hacking, teaching various techniques including exploiting vulnerabilities and privilege escalation.
The video is about ethical hacking and learning to hack.
The first part of the video focuses on exploiting a vulnerability in Jenkins, demonstrating the importance of paying attention to small changes in responses to identify potential security issues.
The second part of the video covers privilege escalation on a Linux machine using directory brute forcing and exploiting a vulnerability in the Navigate CMS.
12:05:55 Learn about ethical hacking in this 12-hour full course. Discover techniques for finding vulnerabilities and escalating privileges.
⚡️ The video demonstrates the process of ethical hacking and provides a step-by-step guide.
🔍 The focus is on finding usernames, passwords, and interesting writable files to exploit.
🛡️ The concept of suid (Set user ID) binaries and their potential for privilege escalation is explained.
You might also like...
Read more on Science & Technology
NC State University - College of Natural Resources - Environmental Sciences Major

Morning Future - Cosimo Accoto: "Vi racconto il futuro digitale che ci aspetta"

Wörter und Sprachen - Automaten und formale Sprachen 1
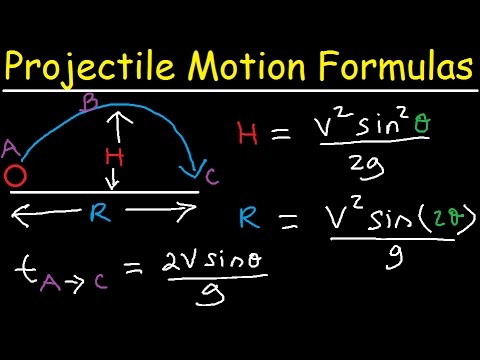
Introduction to Projectile Motion - Formulas and Equations

Vocabulary game with a ball. English classroom
![[Why series] Earth Science Episode 3 - High Air Pressure and Low Air Pressure](https://i.ytimg.com/vi/DquXO2FEl0Q/maxresdefault.jpg)
[Why series] Earth Science Episode 3 - High Air Pressure and Low Air Pressure