DEF CON 31 War Stories - Nuthin But A G Thang - Tracy Mosley
A talk on vulnerabilities in cellular networks, including attacks on authentication protocols, registration processes, and power-saving modes.
00:00:00 Tracy Mosley presents a talk on the evolution of cellular networks, focusing on core networks and vulnerabilities from 2G to 5G.
📺 The video is about the evolution of cellular networks, focusing on cellular core networks.
📶 The talk covers the development and vulnerabilities of different generations of cellular networks, including 2G, 3G, 4G, and 5G.
📡 The network architecture of cellular networks includes components like the mobile station, radio access network, and core network.
00:06:21 This video discusses the evolution of cellular networks, including GSM and GPRS. It explores the architecture and vulnerabilities of these networks, highlighting the lack of mutual authentication and weak encryption schemes.
🔑 Authentication center, secret keys, and registers in cellular networks
📡 Radio access network, base transceiver station, and base station controller
🔒 Security vulnerabilities in GSM, including lack of authentication and weak encryption
💡 Introduction of GPRS, combining circuit-switched and packet-switched functionality
🌐 Serving GPRS support node, gateway GPRS support node, and core network
00:12:45 A presentation on the vulnerabilities in cellular networks and the potential attacks that can be carried out, including encryption bypass and downgrade attacks.
There was a Nokia GGSN attack in Italy and Denmark that disrupted the GPRS network connectivity for a whole area of users.
Cisco threat bulletins provided valuable information about vulnerabilities in core network infrastructure.
In the evolution to 3G and UMTS networks, there were changes in terminology and the addition of new network components.
Mitigations for security issues in 3G included true mutual authentication and improved confidentiality.
Attack vectors in 3G included rogue NodeBs, downgrade attacks, remote IMSI attacks, and HLR overloading.
00:19:10 The video discusses vulnerabilities in cellular networks, including attacks on SGSN and LTE networks. It highlights the evolution of network elements and the need for improved security measures.
Attackers can tie up the SGSN by repeatedly sending resynchronization sequence values.
Attackers can cause a denial of service by generating radio resource control connection requests for valid IMSIs.
LTE evolution introduces a fully-IP based network architecture with evolved packet core.
00:25:35 Attacks on cellular networks can inject fake paging messages and cause panic in a specific area. Implementation errors can lead to info leaks and denial of service. Mitigations include encryption and authentication procedures.
🔒 Attackers can inject fake paging messages causing panic in a specific area through paging channels.
📱 Implementation errors led to a supposedly temporary identifier being permanent, allowing attackers to determine other identifiers and target users nearby.
🔒 Issues with a Cisco Public Data Network Gateway can cause denial of service for the gateway, stopping TCP and SIP connections.
💡 4G networks bring advancements like IPv6 expansions, adaptive modulation, and IP multimedia subsystem.
🔒 Mitigations include encrypting all radio interface data and implementing an authentication and keying procedure for mutual authentication.
🔒 Attack vectors include IMSI-catchers and pre-auth remote attacks on the Cisco ASR 5000 PDN gateway.
00:31:58 The video discusses the evolution of cellular networks to 5G, highlighting changes in network architecture, virtualization, orchestration, network slicing, and security measures. It explores the functions and communication between different components in the network, as well as potential attack vectors in 5G.
📡 The architecture of cellular networks is changing significantly with the introduction of 5G, including network function virtualization, management and orchestration, and network slicing.
📶 The new network architecture includes components such as gNodeB, AMF, SMF, UDM, and PCF, which handle functions like mobility management, session management, and policy control.
🔒 Mitigations in place for 5G security include new identifiers (SUCI and SUPI), larger keys, message protection, and the security anchor function.
⚠️ There are more attack vectors in 5G networks due to the increased number of connected devices.
00:38:20 DEF CON 31 War Stories - Nuthin But A G Thang - Tracy Mosley: A talk on vulnerabilities in cellular networks, including attacks on authentication protocols, registration processes, and power-saving modes.
🔒 An attacker can intercept the plain text transmission of the authentication and keying protocol, allowing them to determine the presence of a target subscriber in a specific cell.
⚡️ The attach request in the registration process can be tampered with, leading to potential attacks such as battery draining and power saving mode manipulation.
🔎 Stream reuse attacks and the use of malicious stream closed identifier can cause server crashes, and vulnerabilities in the mobility management entity have been confirmed by China Unicom.
You might also like...
Read more on Science & Technology
The PERFECT Desk Setup!

You MUST Watch This Before Tackling Problems | Pinhome Dara & Ahmed #eo #Indonesia #property
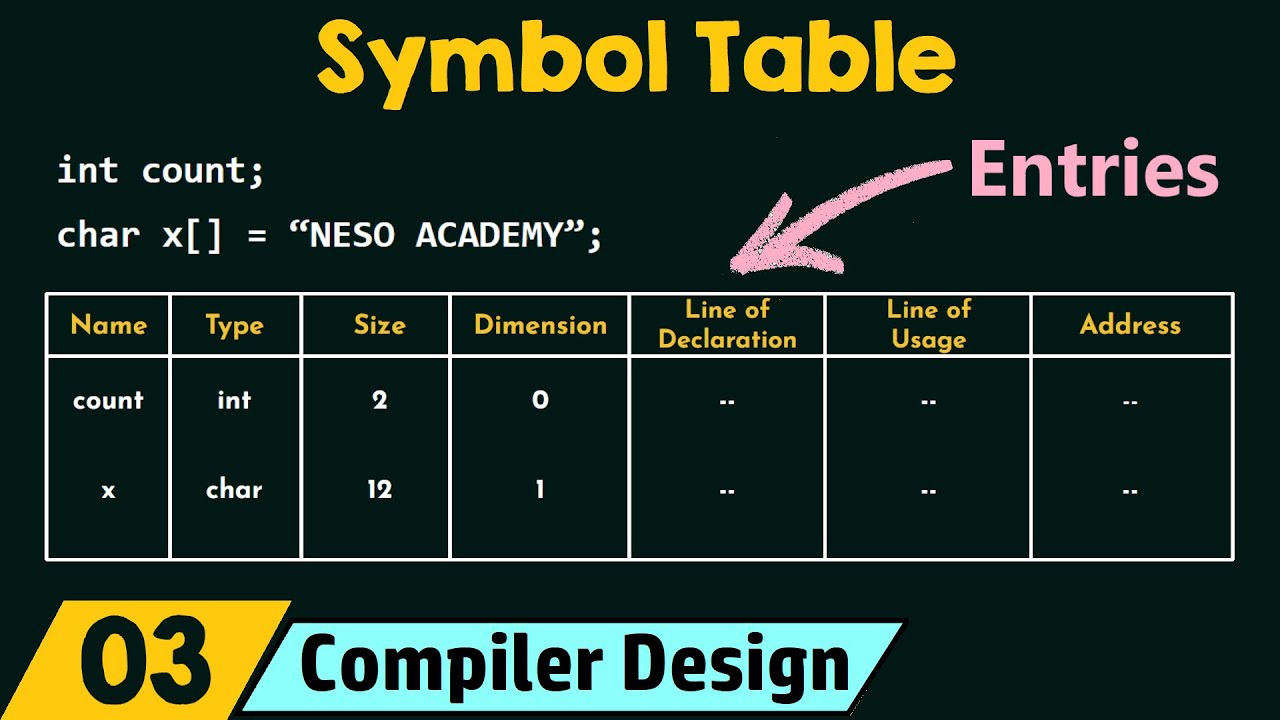
Symbol Table
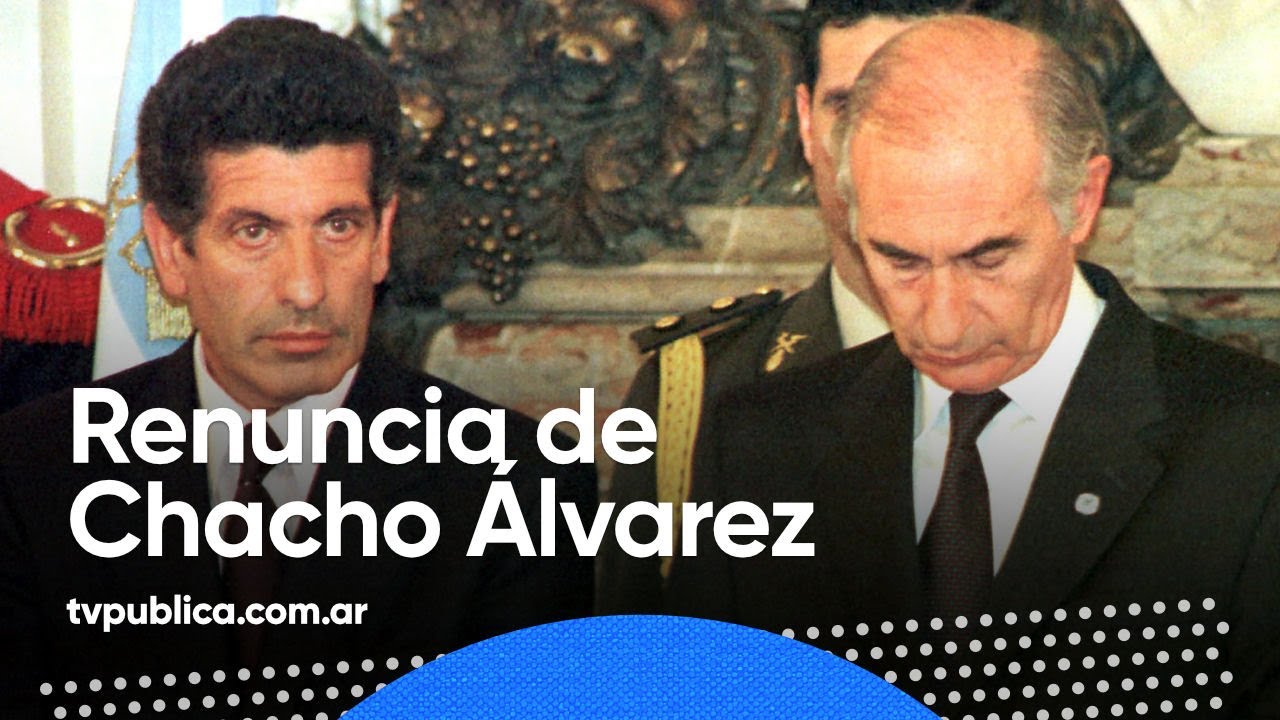
Informe Especial: Renuncia de Chacho Álvarez - 40 Años de Democracia

Decoding India's Economy | With Prof Prabhat Patnaik

The Psychology of Human Misjudgement - Charlie Munger Full Speech